Fingerprint vs Face ID: Which is safer?
To keep your data safe, how should you unlock your device?
Our personal data has never been more precious. Keeping it safe from cybercriminals and those who would maliciously do us wrong is a priority – but it’s not just malware exfiltrating our personal information from devices digitally that we need to be aware of. An old fashioned attack taking data directly from our phones, physically, is also a risk.
The way to stop people accessing our phones and the reams of data about our personal lives, from bank accounts to precious personal photos and the contact details of our friends, is to protect our device. We can elect to use passcodes – but they’re easily guessable, with hackers doing everything from “brute force” attacks where they guess the digits to ensure access, to monitoring where the greasy smudges of our fingerprints lie heaviest on our screens to work out how to crack into them.
Some choose gesture-activated access, where a swipe of a finger across the screen in a certain pattern unlocks the phone. But that too can easily be accessed by hackers with knowledge of the system.
Biometrics are the future of security
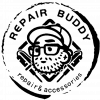
Instead, more of us are relying on two key elements of our biometrics – personal data that in theory only we possess, and no one else. The two main options for those looking to secure their devices seems to be to rely on Face ID, where the front-facing camera on a device is used to cross-check whether your face matches that of the owner of the phone, or a fingerprint.
Both have their benefits and drawbacks. The Apple iPhone has long had Touch ID, where a fingerprint placed on a sapphire crystal capacitive sensor unlocks the phone if the pattern matches. This matching used not just the whirl of your fingerprint, but also elements including the location of your skin’s precise pores to ensure it was you trying to access the device.
But with the iPhone X, Apple removed the home button, and with it, the ability to open your phone with a fingerprint. In its place, it offered something different: Face ID.
Is Face ID secure?
The trade-off was one of convenience and security versus looks. Apple wanted a sleek front to its phone, shorn of the home button that had been the base of the device since its beginning. The alternative it proposed was a more simplistic, but some argue less secure, alternative.
Instead of having to use a fingerprint, device owners could simply point the camera at their own face and unlock their phones. Designed to be a friction-free process, it is considered less secure. Research has shown that it’s possible for strangers who share similar facial features to end up gaining access to strangers’ phones, simply because the technology works on a lower resolution, and unlike fingerprints, facial features aren’t at all unique. Researchers managed to use social media pictures to spoof facial recognition security even before FaceID was released, which is easier than generating fake fingerprints. “Although face recognition is absolutely better than no protection at all, it’s not relatively more secure than Touch ID,” write Forbes.
While it’s not likely to have as catastrophic consequences as many fear, with most accidental unlockings likely to happen between family members, rather than a criminal managing to gain access, the reality is that facial recognition is less reliable than fingerprints for getting access to phones and devices. However, fingerprints have also proven to be able to be hacked, as shown by Marc Rogers at Lookout. “TouchID is strong enough to protect users from casual or opportunistic attackers,” he writes, “and it is substantially better than nothing.”
Therefore, if given the opportunity to buy an Android phone that has facial unlocking or fingerprint security, if you’re after safe use of your phone, it’s likely better to try fingerprints. If you’re after quick and convenient access to your phone, and are happy to trade off some security for that, then relying on Face ID is a passable alternative – but just be careful not to store vital information on your phone where anyone could access it.